How do passkeys work?
- Blog
- How do passkeys work?
Passkeys are quickly replacing passwords as a faster, more secure way to sign in to apps and websites. Instead of typing a password, you verify your identity with a fingerprint, Face ID, or a device PIN. But what's actually happening behind the scenes? Here's how passkeys work, why they're more secure than passwords, and how to start using them.
Passkeys are a secure cryptographic method for authenticating users without passwords, offering better online security and safety while improving ease of use. Once set up, passkeys are easier to use than passwords and exponentially more secure because their strength doesn’t depend on the user.
More and more websites are adopting this passwordless technology, including many big tech companies such as Google, Amazon, Apple, and Microsoft.
Learn more about passkeys in this detailed blog: What are Passkeys?
Passkeys are a form of passwordless authentication that replaces traditional passwords. They can be used on most operating systems within a password manager and leverage public key cryptography that has been under development for more than 10 years. The FIDO Alliance was founded in 2013 to shepherd and drive the technology, ensuring universal, open standards, and is supported by a long list of members and sponsors, including Bitwarden. Passkeys use the WebAuthn cryptographic protocols developed by the alliance, hailed as the gold standard in secure authentication.
At their core, passkeys use public key cryptography to securely replace passwords, and they're quite simple to use.
When a user registers for a new account on a website or app that supports passkeys, they will be asked to create a passkey. When prompted, simply scan the provided QR code with a phone or use a biometric, like a fingerprint or Face ID, to automatically create the passkey.
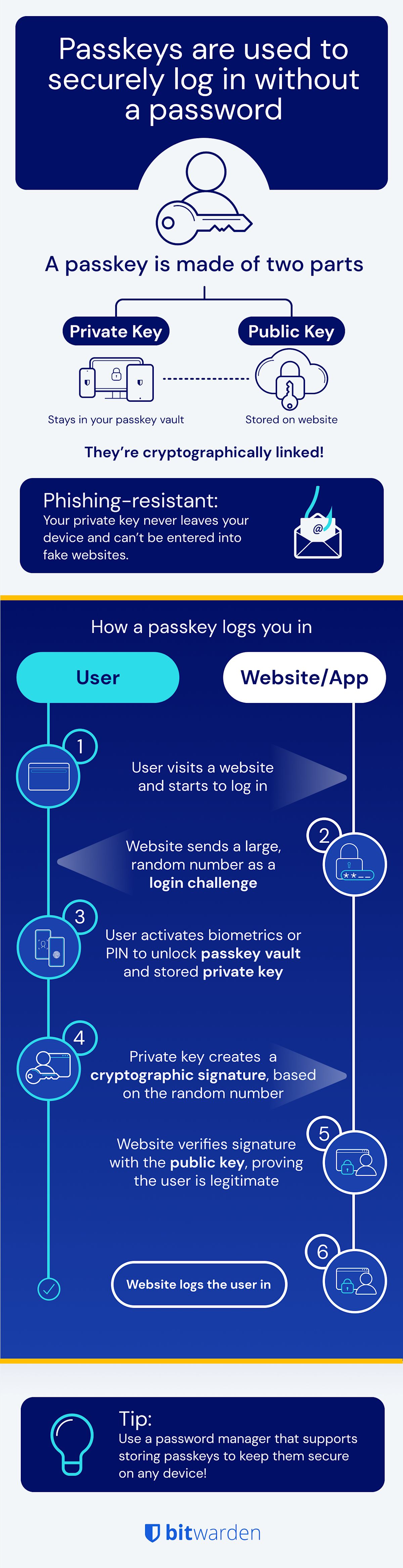
That passkey actually consists of two keys: a public key and a private key. A key is a very long, random string of characters that’s used as a base for cryptographic processes. The public key is stored on the server where the new account is being registered, and the private key is stored on the user's device or in a secure software-based vault. While those two keys differ from each other, they do have a special relationship: one can decrypt messages (private key on a user's device, which is supported by most operating systems) that have been encrypted by the other (public key on the server). That key pair is used to verify and authenticate the user.
To sign in to a passkey-enabled website, the site will send a login challenge — a really large random number — and the user’s private key will use cryptography to “sign” the challenge with a response to it. The website checks the signature against its public key to verify authenticity. Once confirmed, the website grants the account access.
Passkeys are significantly more secure than passwords. One of the most important things about these key pairs is that the private key is secure and never leaves the operating systems on which they are stored, and the password manager keeps it locked through biometrics, PIN, or a password. The public key, on the other hand, could be shared with the world, for example, in the case of a website data breach, and security still would not be compromised so long as the private key remains secure.
Here’s a popular analogy to help understand asymmetric key pairs. The infographic below explains the steps for using a passkey and its key pair to verify a user’s authenticity when logging into a website.
Passkeys are safe. The private key is stored securely on your device or in a password manager vault and is protected by biometric authentication, such as a fingerprint scan or Face ID, or a device PIN. It is never shared with the website and never transmitted over the internet, which means there is no secret for attackers to intercept or steal.
This design makes passkeys resistant to phishing, credential stuffing, and brute-force attacks. Even if a website's servers are breached, the exposed public key cannot be used to gain access to your account. Thanks to the public-private key pair, passkeys are far better equipped to prevent attacks and better ensure user privacy.
Creating a passkey is straightforward. On a website or app that supports passkeys, go to your account's security settings and look for an option to add a passkey. You'll be prompted to verify your identity using a fingerprint, Face ID, or device PIN. Once confirmed, your passkey is created and stored, either on your device or in a password manager like Bitwarden that supports passkey storage.
From that point on, signing in is as simple as using that same biometric or PIN. No passwords to remember, type, or reset.
Bitwarden Password Manager supports creating, storing, and autofilling passkeys across your devices, making it easy to manage them alongside your existing passwords in one secure vault.
Get started today with a free account or share with your team by starting a free business trial.
For developers, Bitwarden Passwordless.dev provides API frameworks to help you build discoverable FIDO credentials such as passkeys.